
In cyber risk, a simplification continues to spread that, while convenient to adopt, struggles to hold up when confronted with the operational reality of infrastructures. Risk is represented as an ordered sum of elements organized in lists that give a sense of control, without actually describing what happens inside an organization. It’s an approach that works well on paper and often satisfies audit and compliance requirements, but leaves exposed precisely the areas where risk tends to concentrate.
This mindset leads to treating vulnerabilities and assets as autonomous units that can be analyzed separately, while in practice every component is embedded in a context of dependencies and behaviors that mutually influence one another. A modern infrastructure develops as a web of relationships in which applications, technologies, and processes intertwine, generating dynamics that never emerge when observing individual elements in isolation.
Even the distinction between IT, OT, and IoT environments progressively loses meaning when looking at how organizations actually function, because these dimensions coexist and interact continuously, giving rise to a complex surface that evolves alongside the business. Risk takes shape within connections, and it is precisely at the intersections between systems that the defining conditions for overall exposure concentrate.
When analysis focuses on individual assets, it is possible to assign a security level based on known configurations and vulnerabilities, producing an assessment that appears coherent and data-driven — as long as it remains confined to that perimeter. The picture changes the moment those same assets are observed within the relationships connecting them to other systems, because it is in that transition that unexpected behaviors and risk pathways emerge that are difficult to intercept through point-in-time analysis. The perimeter, in other words, is an analytical convention that real-world risk is under no obligation to respect.
It can happen that two components considered reliable together generate a critical vulnerability the moment they begin communicating, just as a configuration deemed adequate may, in a different context, help facilitate the propagation of a threat. Equally, a business process may be exposed to conditions that develop along application dependencies outside its direct perimeter, yet still affect its functioning. These are situations that traditional assessments don’t surface, because they require viewing the system as something living — where every change in one part produces effects that ripple elsewhere.
These dynamics make clear that risk manifests as the result of the system’s overall behavior, with characteristics that cannot be traced back to individual elements in isolation. Traditional approaches succeed in describing and classifying components, but struggle to read the network of relationships connecting them — which is precisely where risk develops and consolidates. As long as analysis remains at the level of the individual node, the real problem stays out of focus.
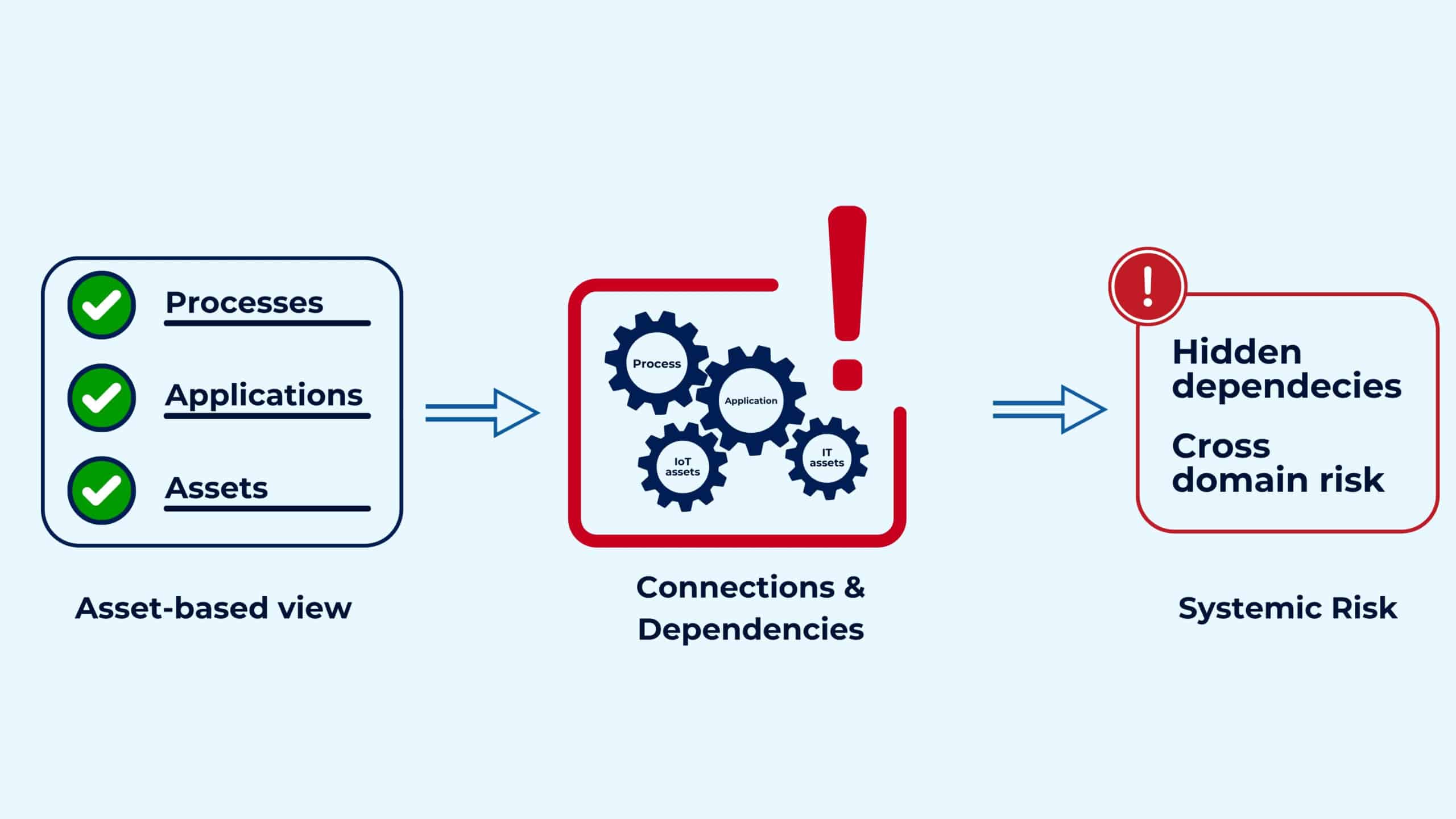
For years, risk was analyzed starting from individual assets, treated as independent elements within a system that was never independent. The most significant threats emerge from the relationships connecting systems, processes, and applications — spreading along pathways that static analysis simply cannot see.
We believe that today, Cyber Risk is an excessively fragmented and predominantly qualitative field — limited to performing static, isolated controls, without an adequate overall view and, above all, without the structured data needed to support decision-making.
Our solution was designed with the goal of reading the complexity of Cyber Risk through the relationships between the elements that make up an infrastructure, with the awareness that a platform of this kind must first and foremost be capable of seeing what fragmented approaches leave in the dark.
Ours is a strictly data-driven model, which allows us to analyze the real relationships between systems and simulate scenarios — observing through data how a threat can propagate within the infrastructure, with the ability to anticipate its effects before they materialize. At the same time, thanks to our agentless approach, we conduct our analyses without interfering with operations, extending assessment even to contexts where operational continuity is essential. Taken together, our ESRA solution delivers a reading of risk that reflects the relational nature of infrastructures and accompanies their evolution over time.
An arrangement that works today guarantees nothing about tomorrow, because all it takes is for one element to shift for every relationship around it to change along with it. This is due to the nature of increasingly complex systems, which don’t stay still long enough to be managed through a static approach.
Sound risk management today requires the ability to maintain a coherent reading of the system as it changes. Those who can see the relationships between parts, follow their evolution, and intervene on pathways before they become risk pathways develop a form of infrastructure governance that holds even when the ground shifts. This is exactly the kind of understanding that ai.esra makes actionable — with one precise objective: to make cyber risk as predictable as credit risk, as insurable as operational risk, and as strategic as ESG metrics.
ai.esra SpA – strada del Lionetto 6 Torino, Italy, 10146
Tel +39 011 234 4611
CAP. SOC. € 50.000,00 i.v. – REA TO1339590 CF e PI 13107650015
“This website is committed to ensuring digital accessibility in accordance with European regulations (EAA). To report accessibility issues, please write to: ai.esra@ai-esra.com”
ai.esra SpA – strada del Lionetto 6 Torino, Italy, 10146
Tel +39 011 234 4611
CAP. SOC. € 50.000,00 i.v. – REA TO1339590
CF e PI 13107650015
© 2024 Esra – All Rights Reserved