
Many security reports presented to the Board of Directors are still built around technical metrics that do not enable decision-makers to fully understand the organization’s real level of exposure. This approach creates a disconnect that directly affects decision-making capabilities, as a system compromise becomes relevant only when operational or financial consequences are already unfolding—at which point the damage is visible and the ability to contain it is significantly reduced.
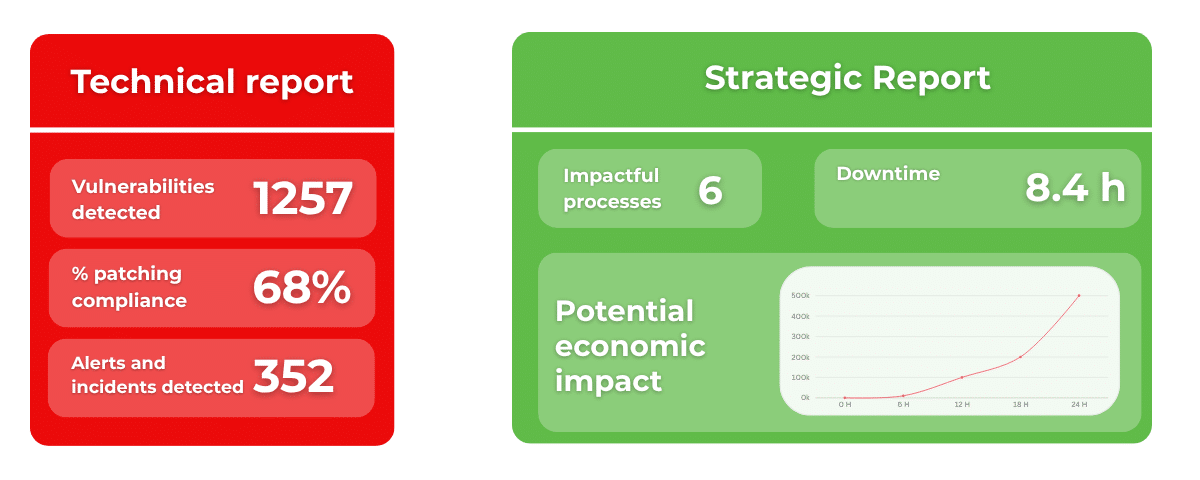
The most common reporting model prioritizes measuring the state of systems through indicators such as identified vulnerabilities, patching levels, or compliance with regulatory frameworks. While these elements are useful for operational management, they are not designed to support strategic decision-making, as they fail to clarify the relationship between a technical condition and its business consequences.
As a result, risk remains confined within the IT domain, making it difficult for the board to interpret and assign it appropriate weight compared to other strategic variables it manages daily.
This disconnect has practical implications for investment decisions. Without an economic interpretation of risk, boards tend to evaluate security as an operational cost rather than a strategic lever. Consequently, resources are allocated based on technical criteria that do not necessarily reflect the areas of greatest exposure for the business.
To make risk management governable at a strategic level, it is essential to understand how a technical event propagates across the organization’s operational chain. Each asset contributes to the execution of one or more processes and, through its interconnections with other systems, creates dependencies that amplify risk—often in unpredictable ways.
The loss of availability of a single asset can disrupt processes that appear unrelated to the original event. In highly interconnected infrastructures, effects propagate through dependencies that traditional reports rarely make visible.
Identifying these dependencies and understanding their role within operational flows allows organizations to assess how an interruption may impact service levels and production capacity. It also introduces a temporal dimension that is often absent in traditional reporting.
Knowing which processes will stop, for how long, and with what financial consequences is the type of information that transforms cyber risk into a variable the board can reason about and act upon.
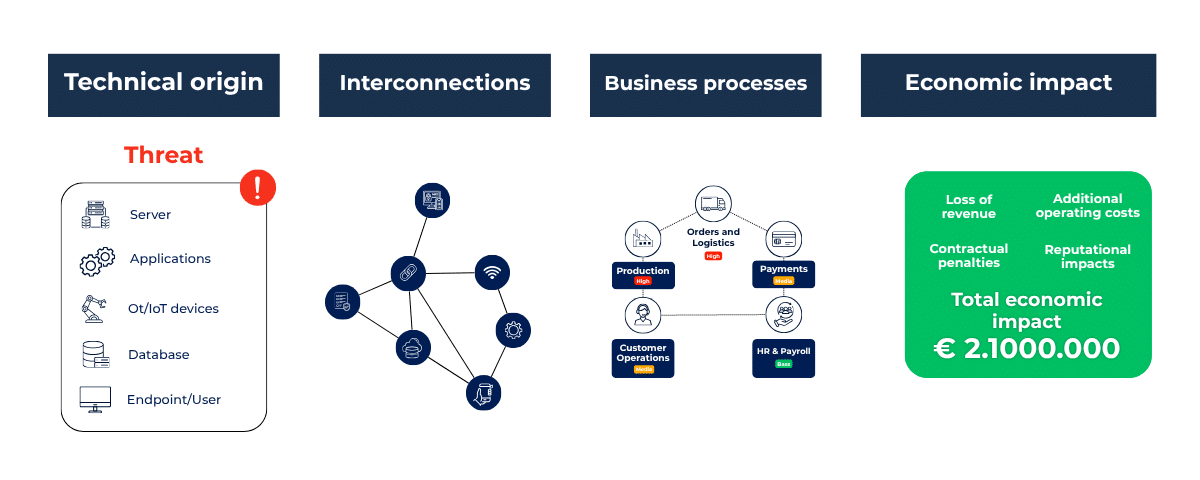
For cyber risk to enter board-level decision-making processes, it must be expressed in economic terms. This requires associating each scenario with an estimate of potential impact, considering variables such as revenue loss, additional operational costs, contractual penalties, and reputational effects that translate into financial consequences over the medium and long term.
This approach makes it possible to compare the cost of mitigation actions with the expected reduction in risk, introducing evaluation logics already well established in other areas of corporate management, where investment decisions are consistently assessed on this basis.
When risk is measurable, organizations can build alternative scenarios, evaluate the effectiveness of different mitigation strategies, and provide the board with a predictive view of risk—similar to what already exists for credit or operational risk.
Cyber risk thus evolves from a difficult-to-assess variable into a quantitative discipline, enabling informed decision-making, rational resource allocation, and the development of protection strategies aligned with business priorities.
Manual analyses or those based on partial inventories are not capable of accurately representing the complexity of modern infrastructures, which are characterized by high levels of interconnection and continuous configuration changes. Any static snapshot quickly becomes obsolete.
For this reason, the availability of complete, real-time, and consistent data on the relationships between system components is the foundation for any business-oriented risk analysis.
ESRA automatically collects this information, reconstructs system relationships, and creates a dynamic model of the infrastructure. This model enables the simulation of risk scenarios, the analysis of threat propagation, and the continuous evaluation of impacts on business processes.
The availability of such models makes it possible to estimate how risk levels change as operational conditions or mitigation strategies evolve. It also aligns technical functions and management around a shared interpretation of risk—an essential prerequisite for truly informed decision-making.
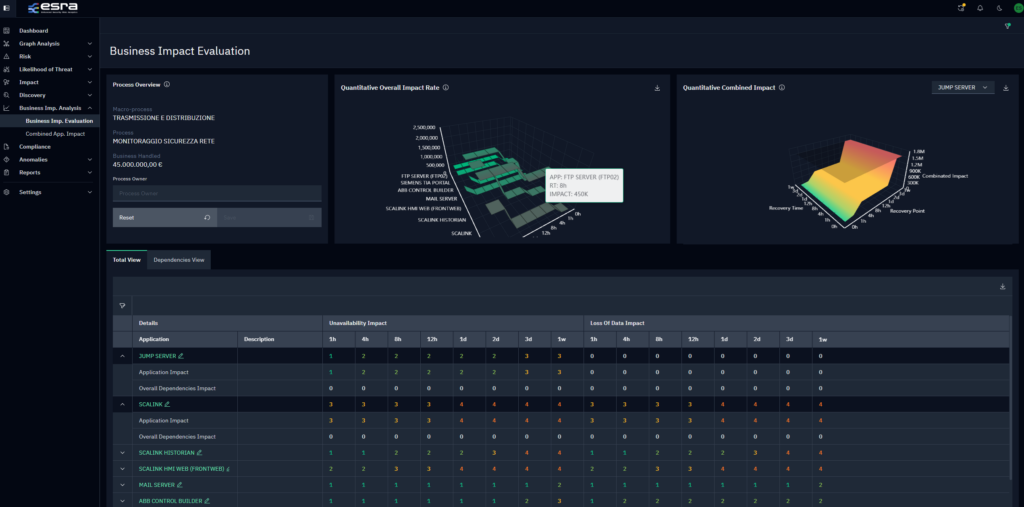
When cyber risk is measured in terms of business impact, the security function changes its role within the organization. The board gains visibility into the areas of greatest exposure and the relationship between investments and risk reduction, while the technical department can focus resources on initiatives that generate the greatest benefit for critical processes, as both are working with the same data and priorities.
ai.esra SpA – strada del Lionetto 6 Torino, Italy, 10146
Tel +39 011 234 4611
CAP. SOC. € 50.000,00 i.v. – REA TO1339590 CF e PI 13107650015
“This website is committed to ensuring digital accessibility in accordance with European regulations (EAA). To report accessibility issues, please write to: ai.esra@ai-esra.com”
ai.esra SpA – strada del Lionetto 6 Torino, Italy, 10146
Tel +39 011 234 4611
CAP. SOC. € 50.000,00 i.v. – REA TO1339590
CF e PI 13107650015
© 2024 Esra – All Rights Reserved